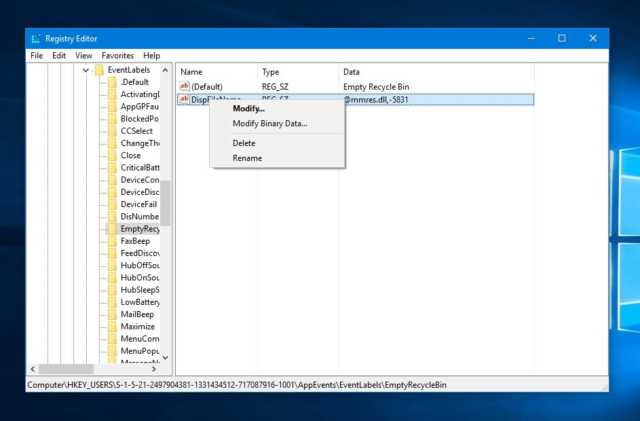
Simple Registry Hacks Bypass Windows Digital Signature, Opening Gates For Malicious Code
Windows Digital Signature check is a mechanism included in Microsoft Windows to make sure that the software or driver you’re trying to install is signed by a trusted entity, andRead More →