Second Researcher Drops Router Exploit Code After D-Link Mishandles Bug Reports
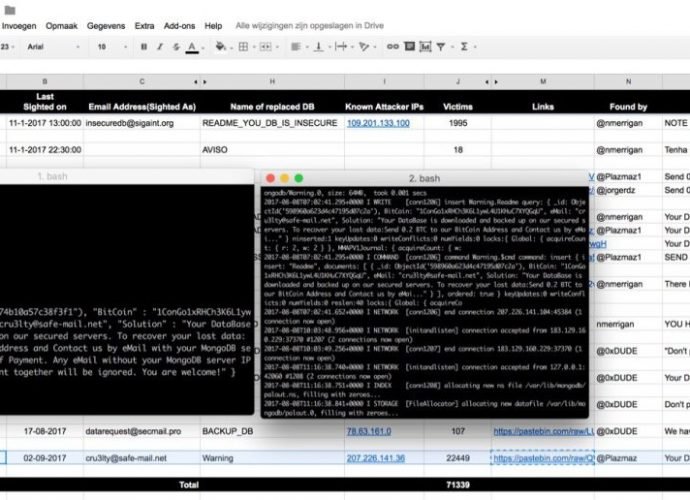
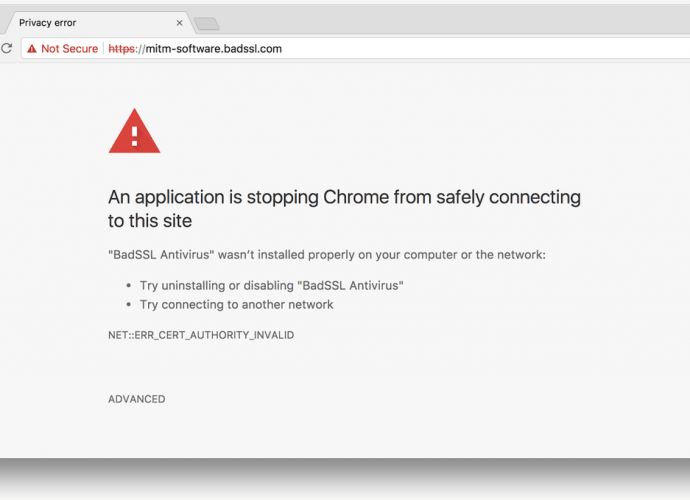
Embedi, a hardware security firm, has published details about two vulnerabilities that have yet to be patched in the firmware of D-Link routers. This marks the second incident of thisRead More →