Hacker “Incursio” Gets Two Years in Prison for Hacking CIA, DHS, DOJ, and FBI
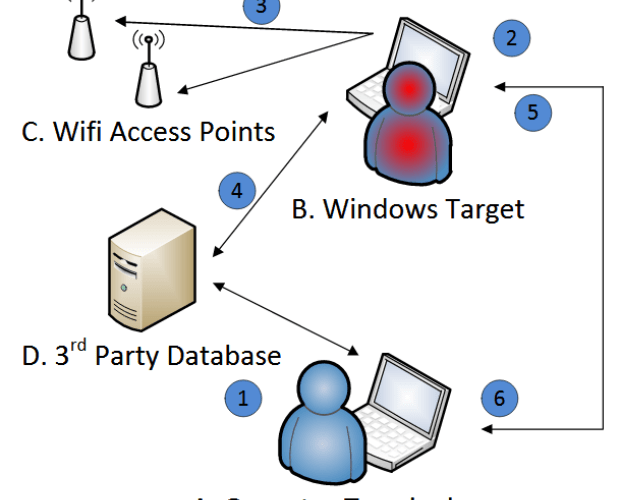
A young man guilty of hacking several three-letter US agencies has been sentenced today to two years in prison, according to a press release from the Department of Justice. AndrewRead More →