New (but Old) Technique Hijacks User Sessions on All Windows Versions
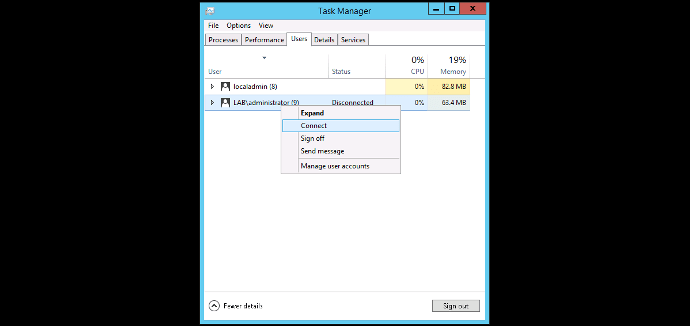
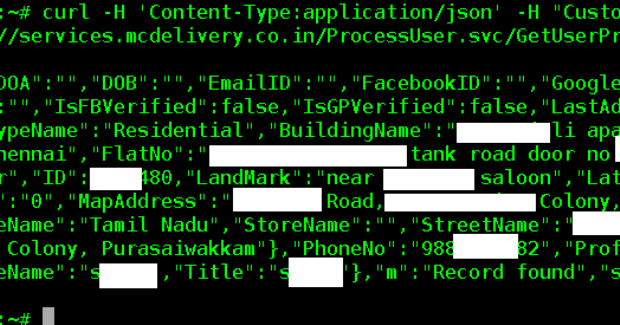
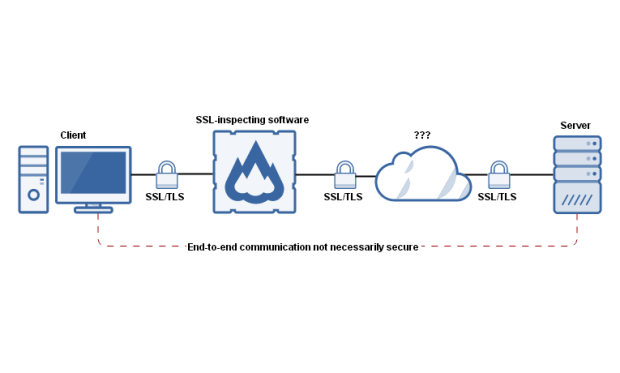
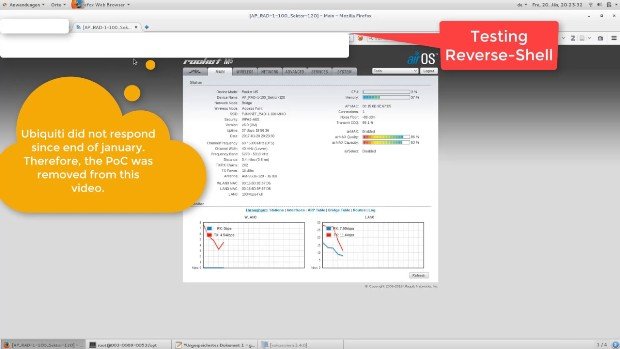
A security researcher has detailed a way to log into any account on the same computer, even without knowing its password. The trick works on all Windows versions, doesn’t requireRead More →