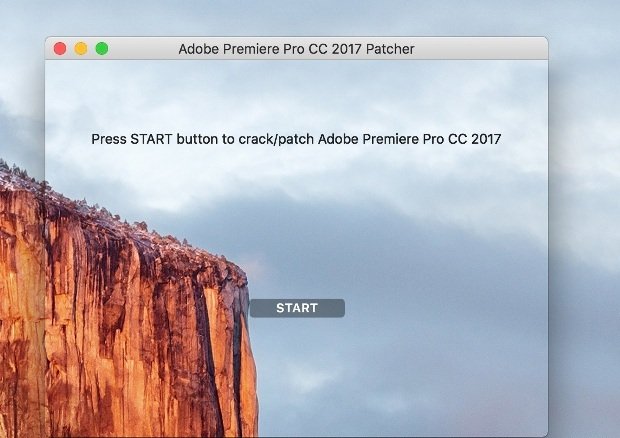
New macOS Patcher Ransomware Locks Data for Good, No Way to Recover Your Files
A newly discovered ransomware family calling itself Patcher is targeting macOS users, but according to security researchers from ESET, who discovered the ransomware last week, Patcher bungles the encryption processRead More →