Attacking JavaScript Web Service Proxies with Burp
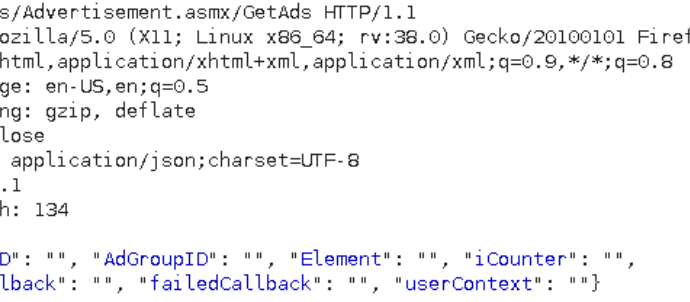
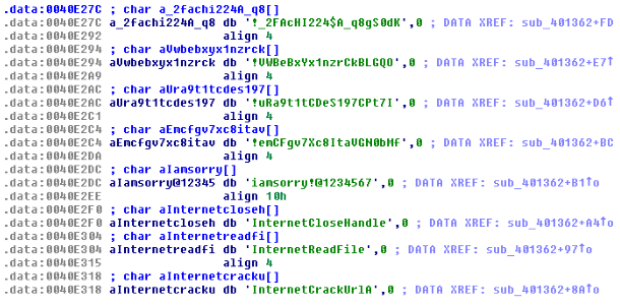
JavaScript Web Service Proxies are an alternative to WSDL (Web Services Description Language) files for interacting with WCF Web Services. The proxy files function as a description of the webRead More →