Now sites can fingerprint you online even when you use multiple browsers
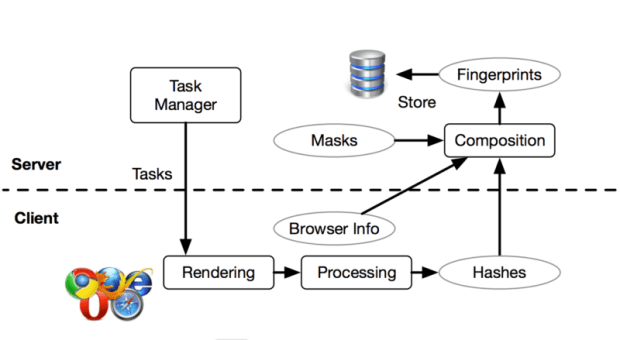
Online tracking gets more accurate and harder to evade. Researchers have recently developed the first reliable technique for websites to track visitors even when they use two or more differentRead More →