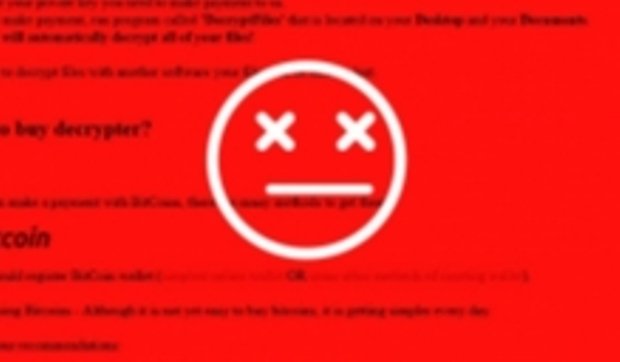
Misconfigured Server Gives Insight Into Cerber Ransomware Operation
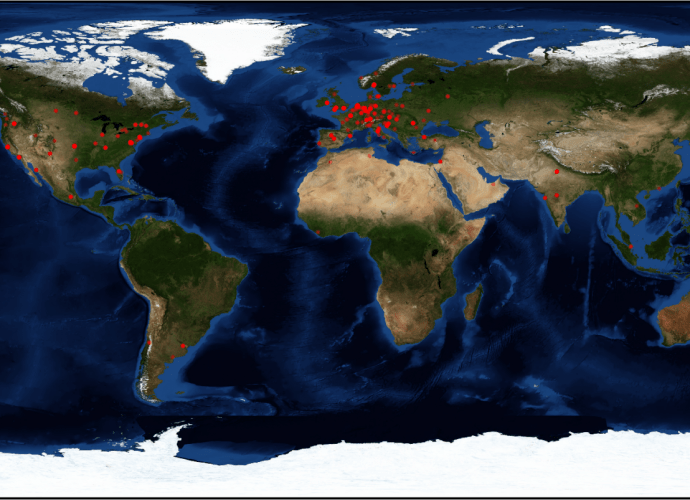
Security researchers have gained access to one of the servers used by the Cerber gang, from where they were able to extract basic statistics about their operation. A security researcherRead More →