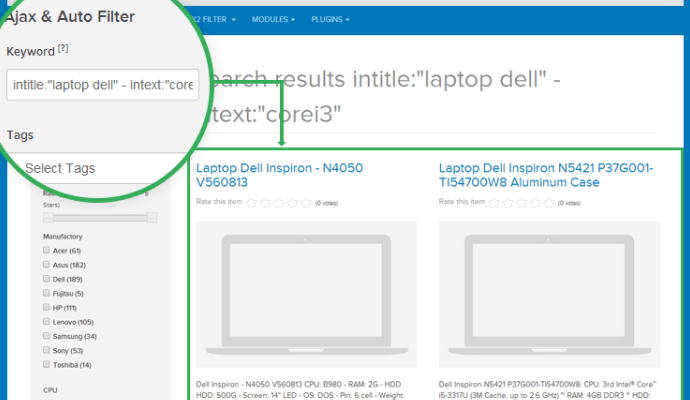
SQL Injection zero-day in component ja-k2-filter-and-search of Joomla
Information Security experts have discovered an SQL injection zero-day vulnerability in Joomla component ja-k2-filter-and-search. Information Security Researchers Dimitrios Roussis and Evangelos Apostoloudis have discovered an SQL injection vulnerability in componentRead More →