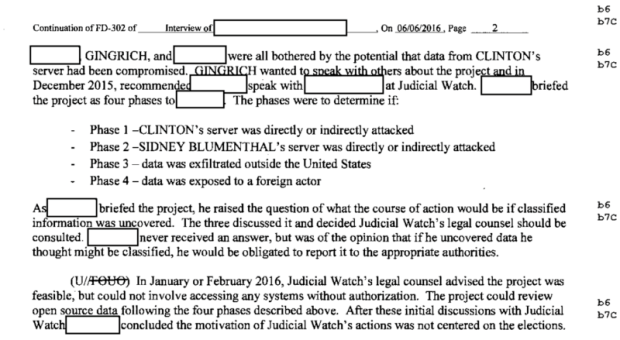
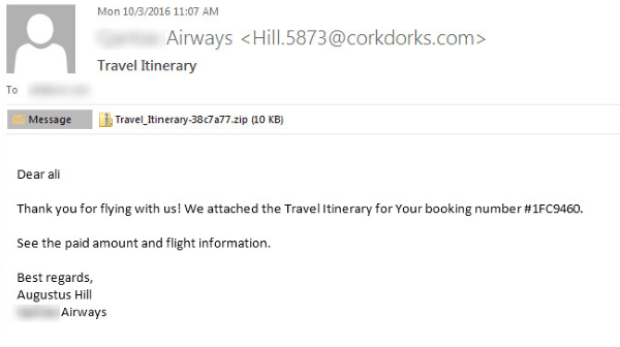
Defense contractor “white hat” tells FBI that Judicial Watch paid him to hunt for Clinton hack
Newt Gingrich brokered deal for moonlighting contractor to hunt for potential breach. More records from the Federal Bureau of Investigation’s review of Hillary Clinton’s e-mail practices have been released throughRead More →