“Hacked” e-mail account of White House worker exposed in 2013 password breach
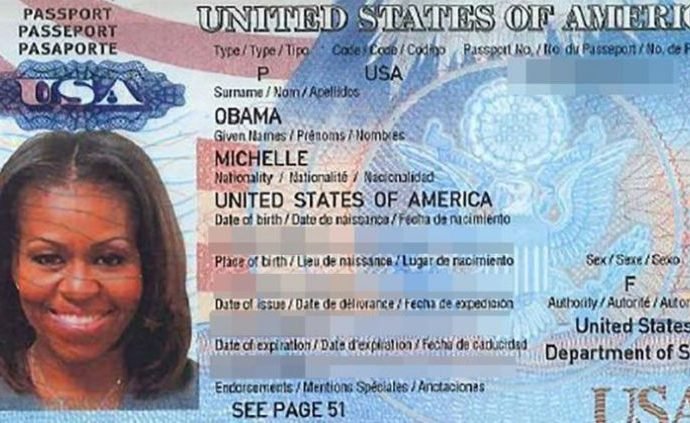
Ian Mellul used Gmail (exposed in Adobe breach) to plan travel for First Lady, Biden.On September 21, a dump of an e-mail account belonging to a White House contractor wasRead More →