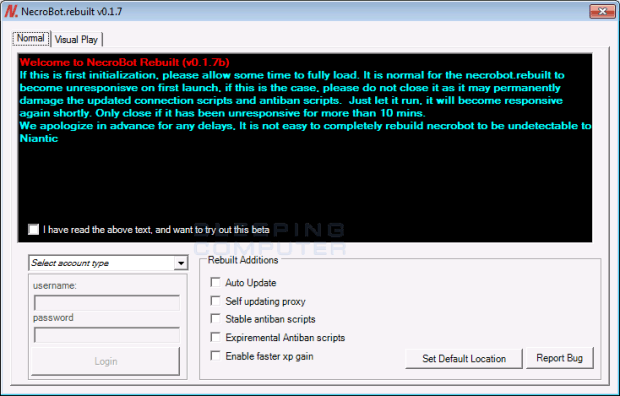
The Nullbyte Ransomware pretends to be the NecroBot Pokemon Go Application
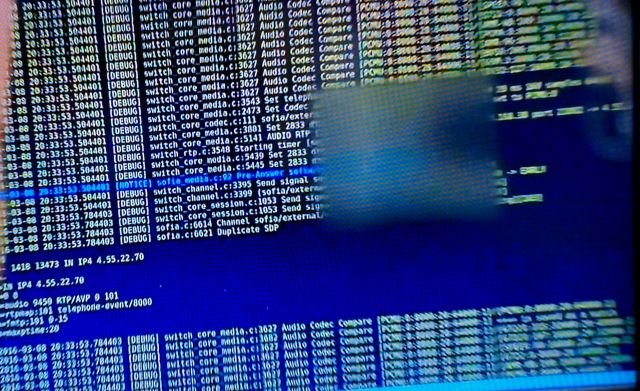
A new DetoxCrypto Ransomware variant called the Nullbyte Ransomware has been discovered by Emsisoft security researched xXToffeeXx that pretends to be the popular Pokemon Go bot application called NecroBot, When infected, the ransomware will encrypt aRead More →