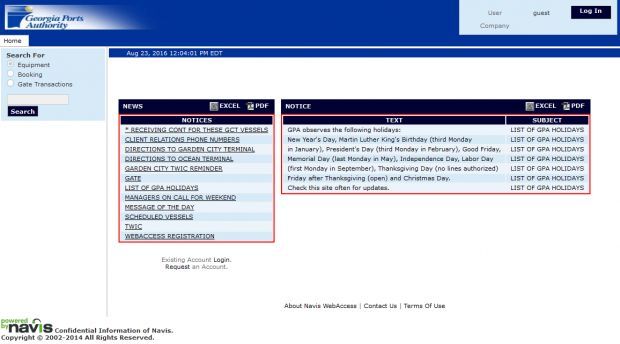
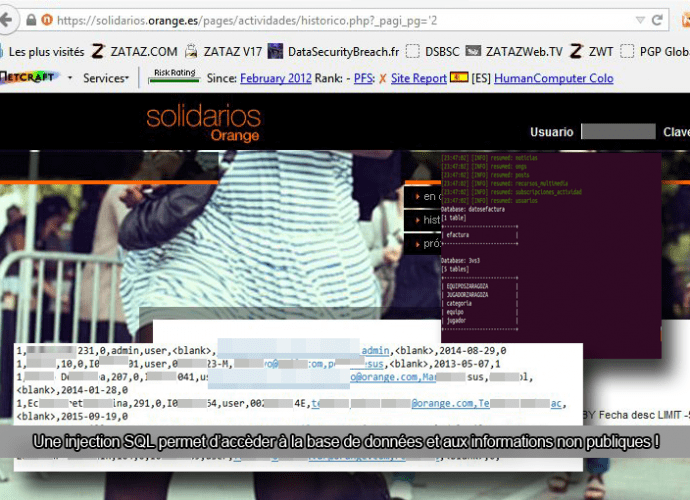
Navis WebAccess app used by US Ports is affected by a SQL injection flaw
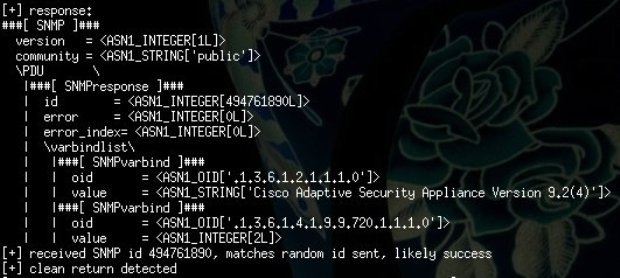
The Navis WebAccess application used in the transportation sector worldwide is affected by a high severity SQL injection vulnerability. A software used in the US ports is affected by aRead More →