Mastercard armours its contactless cards against relay attacks
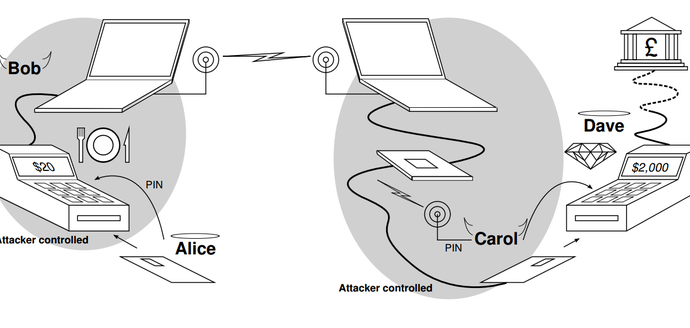
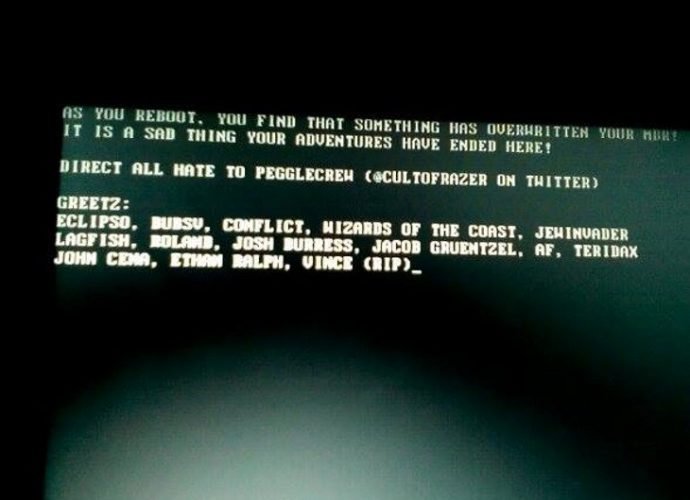
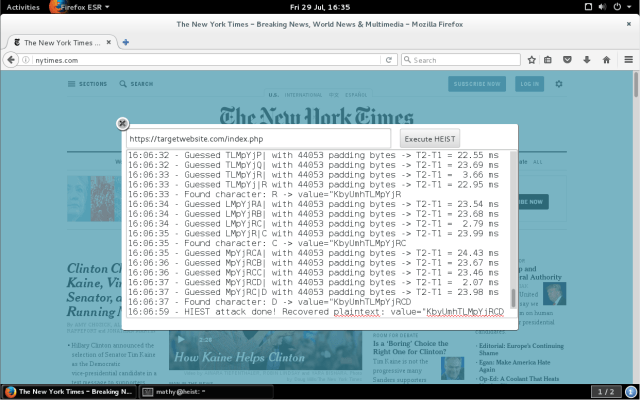
Contactless card payments are fast and convenient, but convenience comes at a price: they are vulnerable to fraud. Some of these vulnerabilities are unique to contactless payment cards, and othersRead More →