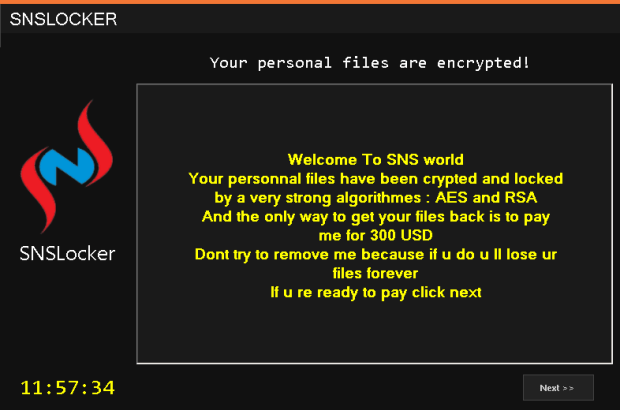
Zcrypt Expands Reach as ‘Virus Ransomware’
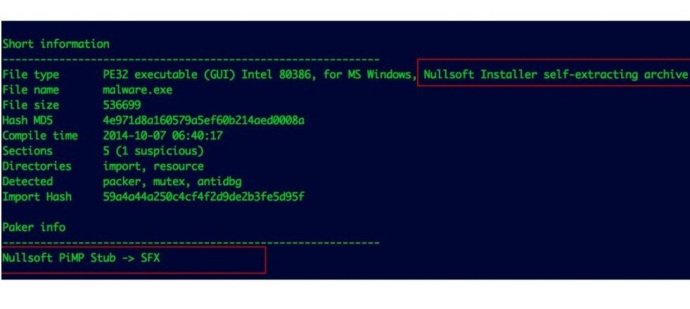
Intel Security has recently seen a new kind of ransomware–Zcrypt—that can self-replicate. This “virus ransomware” arrives via email in a malicious attachment or by usurping an Adobe Flash Player installation.Read More →