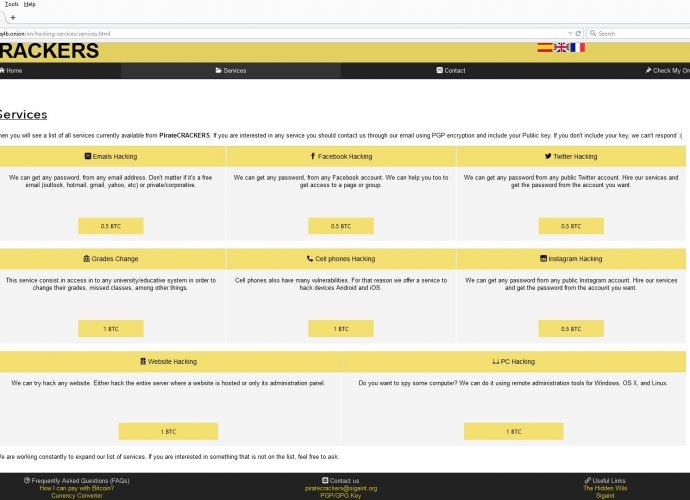
Shuttered Instagram holes opened 20 million accounts to hijack
Phone numbers exposed in borked verification portal Security consultant Arne Swinnen says Instagram has shuttered brute force authentication holes that allowed hijacking of some 20 million accounts. The NVISO infosecRead More →