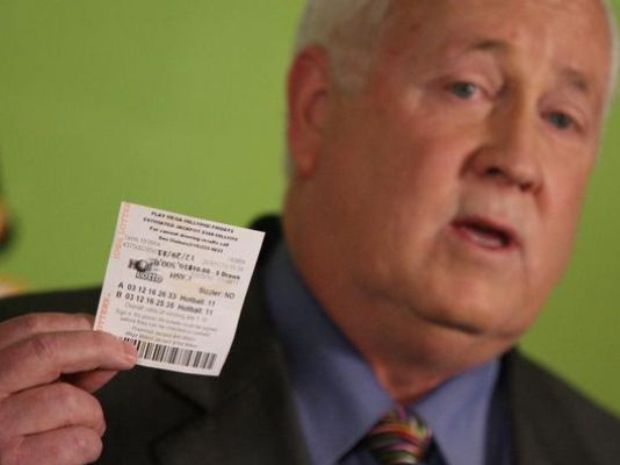
Lottery security director hacked random-number generator to rig lotteries
New evidence collected by prosecutors shows lottery machines were rigged to generate predictable numbers on specific days of the year. Last year, the security director of a US lottery was discoveredRead More →