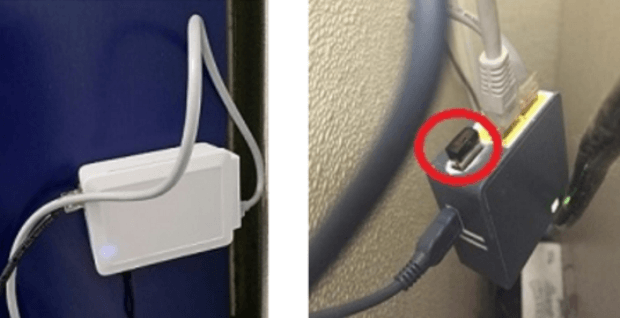
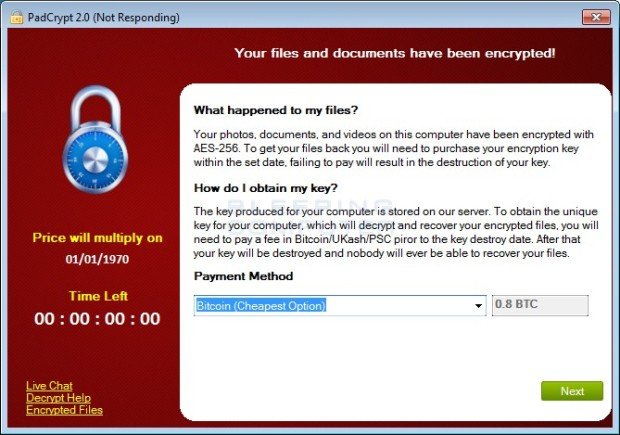
GCHQ is allowed to hack into computers and smartphones
GCHQ is legally allowed to hack into computers, tablets and smartphones owned by the public, a tribunal has ruled, after a legal challenge was brought by Privacy International. The InvestigatoryRead More →