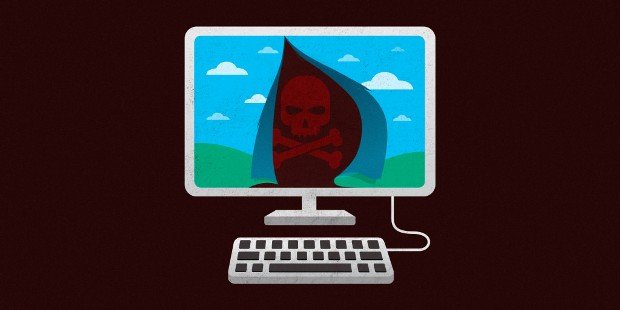
Steam tightens trading security amid 77,000 monthly account hijackings
Traded items will be “held” for days unless you have two-factor security. Account theft is a common and longstanding problem for all kinds of online gaming services, as I canRead More →