Windows Phone hacked! Unlock Lumia bootloader, get root access, flash custom ROMs
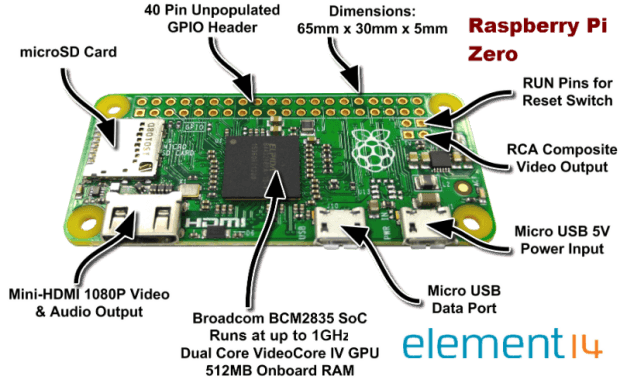
If you are the type of person that likes to tinker, Linux-based operating systems are for you. You would probably have many hours of fun playing with an Android device orRead More →