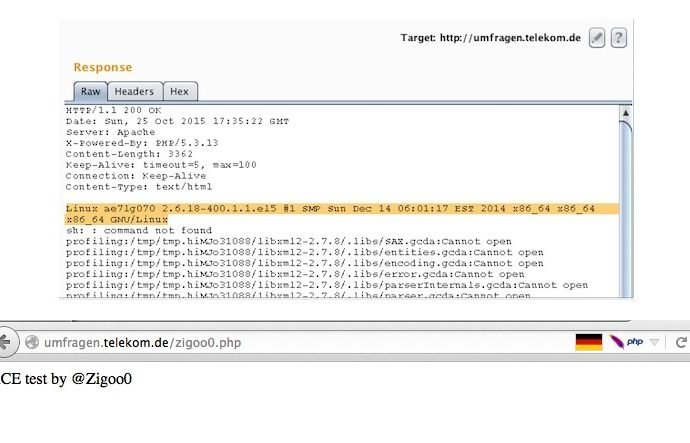
RCE Vulnerability Fully Compromises Deutsche Telekom Server
Attackers could have had full control over DT’s Web server. Independent Egyptian security researcher Ebrahim Hegazy has found another vulnerability, and this one affected the Web servers of Deutsche Telekom, Germany’sRead More →