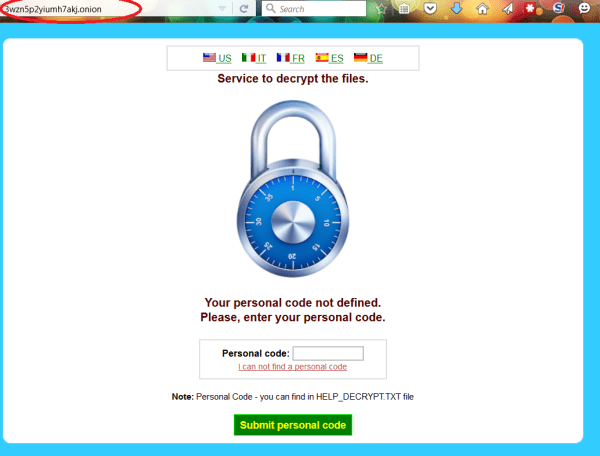
CryptoWall 4.0 released with new Features such as Encrypted File Names
CryptoWall 4.0 has been released that displays a redesigned ransom note, new filenames, and now encrypts a file’s name along with its data. We were alerted to this new variant by variousRead More →