vBulletin password hack fuels fears of serious Internet-wide 0-day attacks
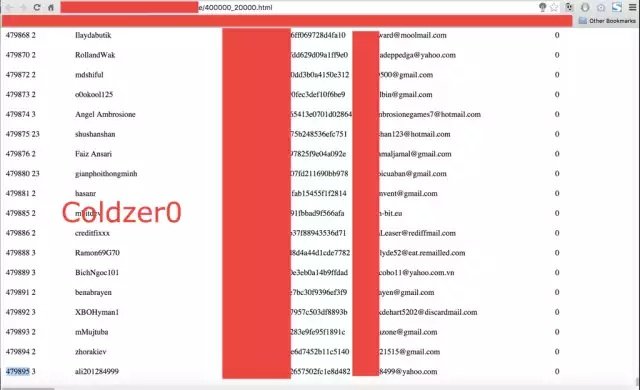
Software maker issued security patch hours after reports surfaced it was breached. Developers of the vBulletin software package for website forums released a security patch Monday night, just hours afterRead More →