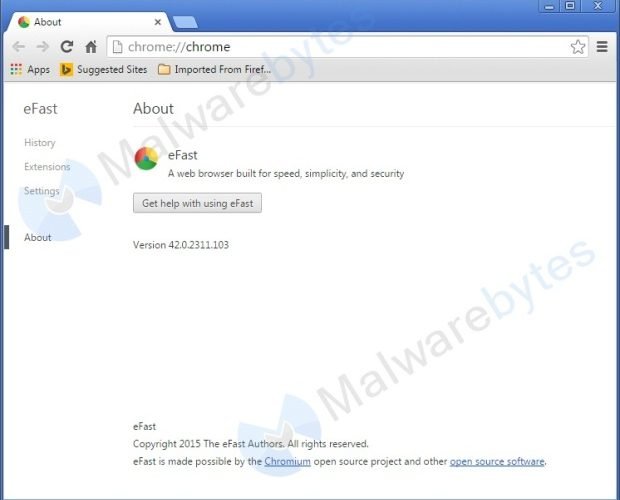
Support scams that plagued Windows users for years now target Mac customers
Swindlers impersonate Apple service that remotely accesses user desktops. For years, scammers claiming that they’re “calling from Windows” have dialed up Microsoft customers and done their best to trick themRead More →