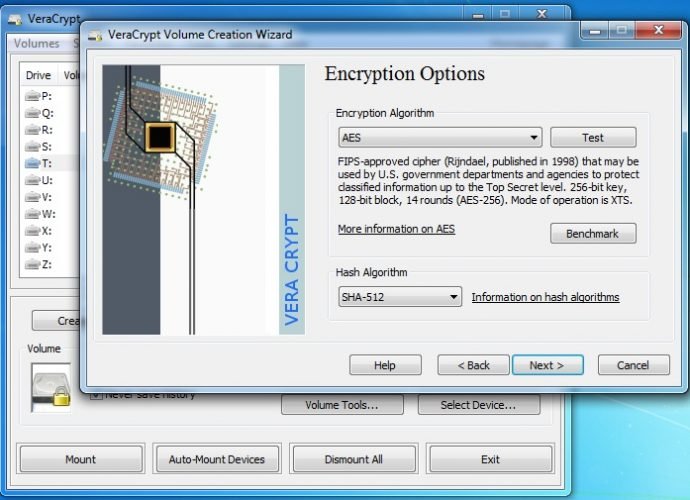
VeraCrypt 1.15 fixes two recently reported TrueCrypt vulnerabilities
Yesterday’s update of the encryption software VeraCyrpt fixed two vulnerabilities that security researcher James Forshaw discovered in TrueCrypt’s source code. TrueCrypt, which has been abandoned by its developers, is stillRead More →