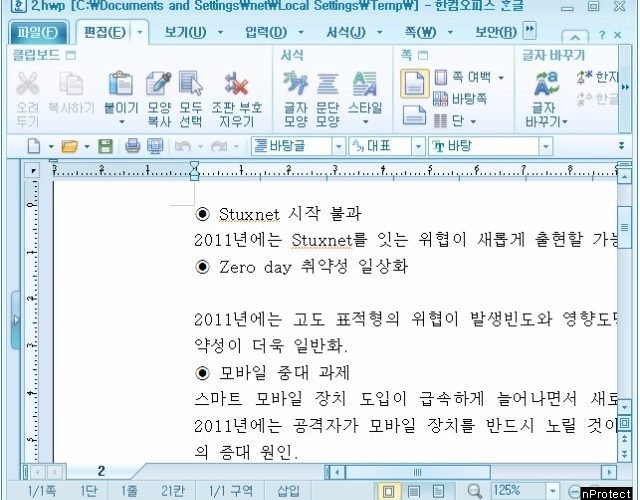
North Korea Installs Backdoor in South Korea’s Favorite Word Processor
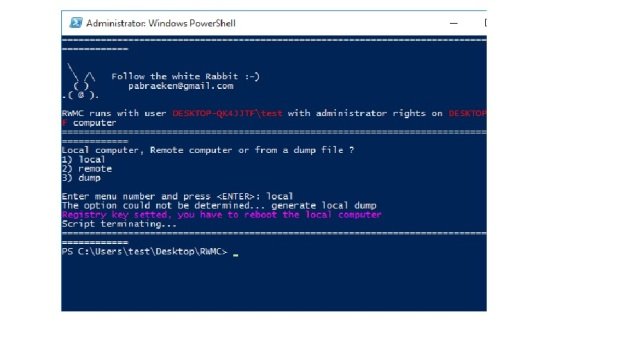
Hackers linked to known North Korean attack points and methods exploited a zero-day vulnerability in the Hangul Word Processor (HWP), widely deployed in the offices of the South Korean government.Read More →