Researchers for the new ‘Hacker’s Playbook’ analyzed 4 million breach methods from an attacker’s point of view to gauge the real risks today to enterprises.
No organization is immune to the risk of a data breach. Security leaders who want to assume the strongest protection must analyze their security posture from a hacker’s point of view to understand risk, validate security controls, and prioritize resources.
That is the premise behind the SafeBreach Hacker’s Playbook, which was released in its second edition today. The first edition of the playbook, published in January, details enterprise security threats and risky habits from the point-of-view of an attacker.
Researchers at SafeBreach “play the hacker” by deploying simulators that assume the role of a “virtual hacker” across endpoints, network, and the cloud. The new Hacker’s Playbook incorporates a total of 3,985,011 breach methods, all executed between January and September 2016.
SafeBreach’s research team had two main objectives in compiling this playbook, says CTO and co-founder Itzik Kotler.
The first is to take highly publicized breaches such as those at Sony and Target, and to create artificial models so customers can better understand these attacks and how they happen. Researchers also figure out how to attack; they analyze different methods to create simulation events to give users a better idea of the threats they face.
“They’re [the researchers] pushing the envelope in creating new ideas and experimenting with existing ones,” says Kotler. “It’s all to show customers what kind of malicious ideas exist.”
Successful breaches are sorted into three pillars: infiltration, how hackers enter a machine; lateral movement, how they jump from one server to the other, for instance; and exfiltration, how they steal valuable data out of the victim organization.
The top infiltration methods used by attackers, according to the report, involved hiding executable files inside non-executable files. Specifically, executable files embedded within Windows script files, macros, and Visual Basic had great success.
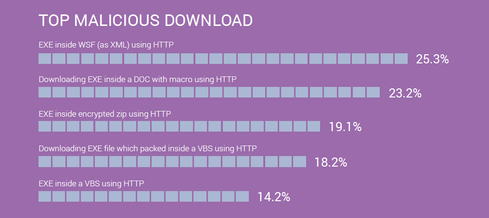
(Image: SafeBreach)
Old exploit kits, many of which have been around for a year or longer, are still considered effective means of delivering malware. These kits challenge endpoint security and secure web gateway products; top picks include Sweet Orange, Neutrino, and Rig Exploit Kit.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











