Latest Vault7 release exposes network-spying operation CIA kept secret since 2007.
Home routers from 10 manufacturers, including Linksys, DLink, and Belkin, can be turned into covert listening posts that allow the Central Intelligence Agency to monitor and manipulate incoming and outgoing traffic and infect connected devices. That’s according to secret documents posted Thursday by WikiLeaks.
CherryBlossom, as the implant is code-named, can be especially effective against targets using some D-Link-made DIR-130 and Linksys-manufactured WRT300N models because they can be remotely infected even when they use a strong administrative password. An exploit code-named Tomato can extract their passwords as long as a default feature known as universal plug and play remains on. Routers that are protected by a default or easily-guessed administrative password are, of course, trivial to infect. In all, documents say CherryBlossom runs on 25 router models, although it’s likely modifications would allow the implant to run on at least 100 more.
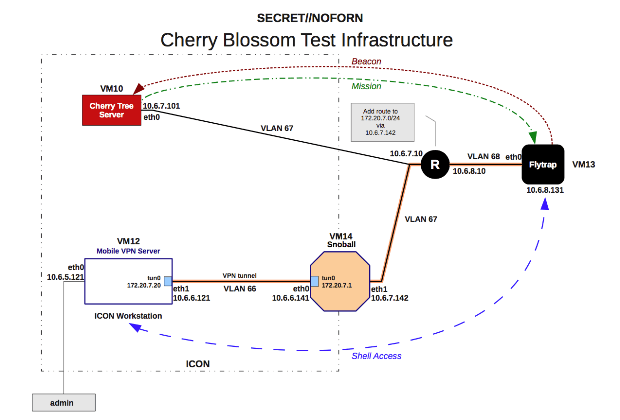
The 175-page CherryBlossom user guide describes a Linux-based operating system that can run on a broad range of routers. Once installed, CherryBlossom turns the device into a “FlyTrap” that beacons a CIA-controlled server known as a “CherryTree.” The beacon includes device status and security information that the CherryTree logs to a database. In response, the CherryTree sends the infected device a “Mission” consisting of specific tasks tailored to the target. CIA operators can use a “CherryWeb” browser-based user interface to view Flytrap status and security information, plan new missions, view mission-related data, and perform system administration tasks.
Missions can target connected users based on IPs, e-mail addresses, MAC addresses, chat user names, and VoIP numbers. Mission tasks can include copying all or only some of the traffic; copying e-mail addresses, chat user names, and VoIP numbers; invoking a feature known as “Windex,” which redirects a user’s browser that attempts to perform a drive-by malware attack; establishing a virtual private network connection that gives access to the local area network; and the proxying of all network connections.
All the communications between the FlyTrap and the CIA-controlled CherryTree, with the exception of copied network data, is encrypted and cryptographically authenticated. For extra stealth, the encrypted data masquerades as a browser cookie in an HTTP GET request for an image file. The CherryTree server then responds to the request with a corresponding binary image file.
A decade of hacking routers

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.