Apache HTTP managers recommend users keep their deployments up to date due to the recent detection of an actively exploited vulnerability. Tracked as CVE-2021-40438, the flaw was described as a server-side request forgery (SSRF) exploited on httpd web servers with mod_proxy module enabled.
According to the report, the vulnerability can be exploited by threat actors using a specially designed request to force the forwarding of requests to an arbitrary server beyond the control of the victims. The flaw was detected by the Apache HTTP security teams during the investigation of another security bug, which made it possible to identify that this flaw resides in all versions prior to 2.4.48.
“By sending a specially crafted request, it is possible to force module mod_proxy to route connections from a source server set up by hackers, allowing the extraction of sensitive information or access to internal servers,” the administrators’ report states.
So far around 500,000 servers have been identified using vulnerable versions of httpd, although Apache mentions that services such as Amazon Web Services (AWS), Microsoft Azure and Google Cloud have additional security mechanisms, so only users managing only httpd servers could be affected.
Multiple proof-of-concept (PoC) exploits have already been published, and some cases of active exploitation have already been recorded. A Cisco report points to the detection of five vulnerabilities in Apache HTTP that affect some of its products, including Prime Collaboration Provisioning, Security Manager, Expressway and TelePresence Video Communication Server.
Moreover, the company also notes that its product safety incident response team was notified about multiple exploitation attempts related to CVE-2021-40438. The cybersecurity authority in Germany has also reported cases of active exploitation, so it is a confirmed fact that at least one hacking group is behind the CVE-2021-40438 attacks.
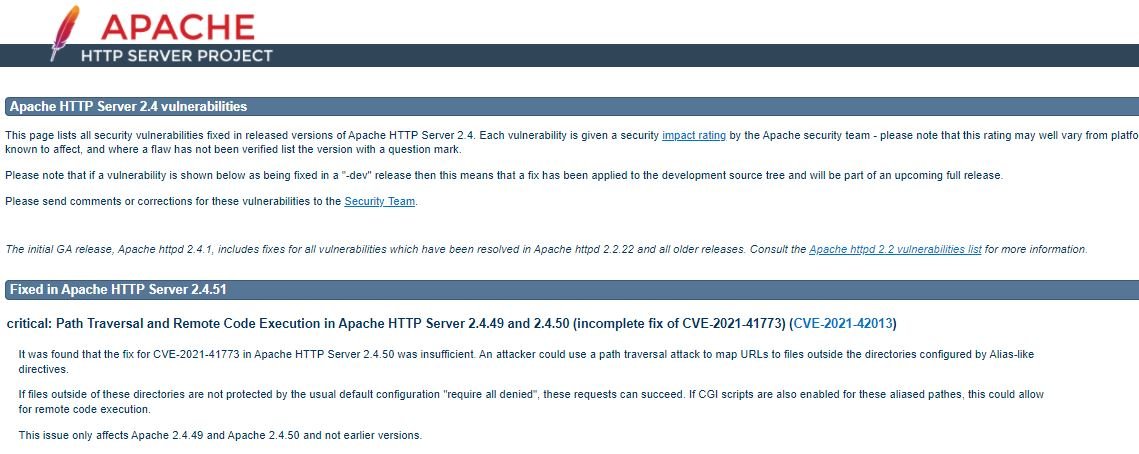
Updates are now available, so users of affected deployments are invited to upgrade to Apache HTTP version v2.4.49.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











