A security report indicates that the developer of the node-ipc JavaScript library, used by the vue.js framework, intentionally introduced a critical vulnerability that could prove disastrous for some users. Brandon Nozaki Miller, also known as RIAEvangelist, created node-ipc, describing it as a cross-process communication module for Node, supporting UNIX, TCP, TLS, and UDP sockets.
Apparently, Miller intentionally changed his code to overwrite the host system data, in addition to modifying the code to display a message calling for world peace, as a protest against the war in Ukraine. GitHub confirmed that this is actually a critical vulnerability tracked as CVE-2022-23812: “Malicious code is capable of overwriting arbitrary files depending on the user’s geographic location,” the platform notes.
At the beginning of March, node-ipc versions 10.1.1 and 10.1.2 were released. When imported as a dependency and executed, these versions of the library check whether the IP address of the host machine is associated with Russia or Belarus; if so, all files are overwritten with a heart symbol.
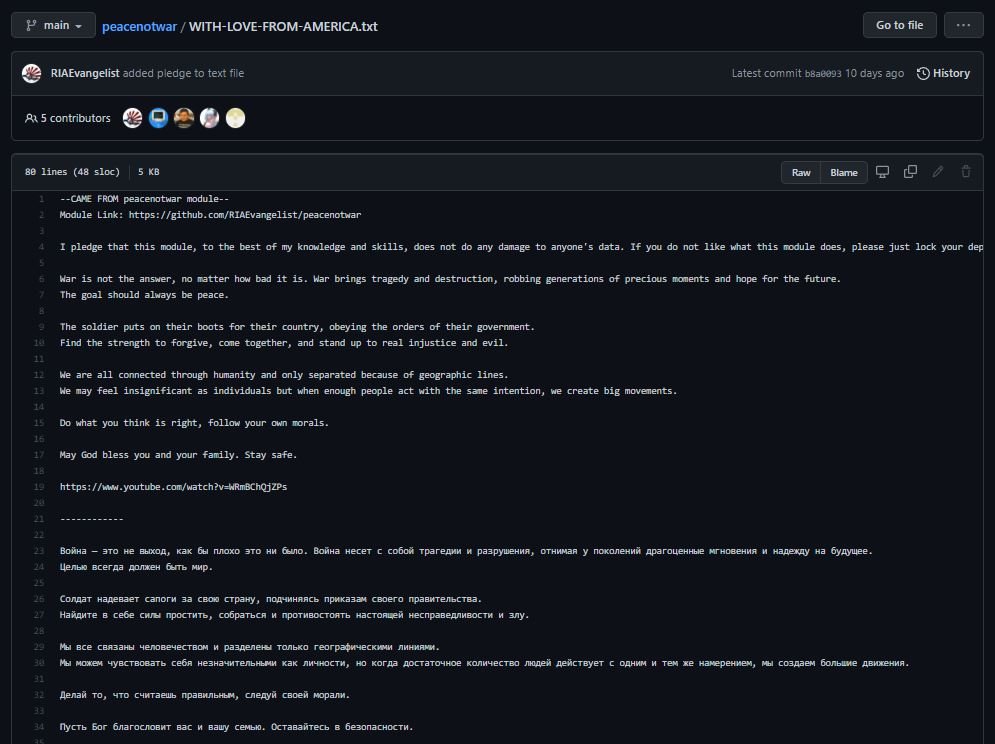
These versions contained a package created by Miller identified as peacenotwar, capable of creating a file called WITH-LOVE-FROM-AMERICA.txt on users’ desktops and in OneDrive folders. The file allegedly contains a phrase from the developer clamoring for peace, although some users who have seen the file claim that it is simply an empty text file.
Whenever another project uses node-ipc versions 11 or 9.2.2 as a dependency, peacenotwar runs, leaving files on users’ computers. Version 9.2.2 has disappeared from the NPM registry along with the destructive versions 10.1.x. Vue.js, for example, brought node-ipc 9.2.2 while it was available, as 9.x is considered a stable branch, meaning there was a period when some Vue developers may have experienced the sudden appearance of text files.
The good news is that few people were exposed to this destructive version of the library, as large applications and frameworks will have used the stable branch. Any user who has accessed the latest generation versions could have lost their files or found the manifest created by the developer.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











