A researcher has detected a critical vulnerability in some of the most common malware and ransomware variants today and whose exploitation would allow interrupting file encryption on infected systems, preventing successful attacks. Among the ransomware strains affected by this flaw are dangerous variants such as AvosLocker, Conti, LockBit, REvil, and the recently detected Black Basta.
The researcher, identified as hyp3rlinx, analyzed these and other malware variants, finding that some of the samples were vulnerable to a DLL hijacking attack, usually employed by threat actors to inject malicious code into a vulnerable application. The report was shared with BleepingComputer.
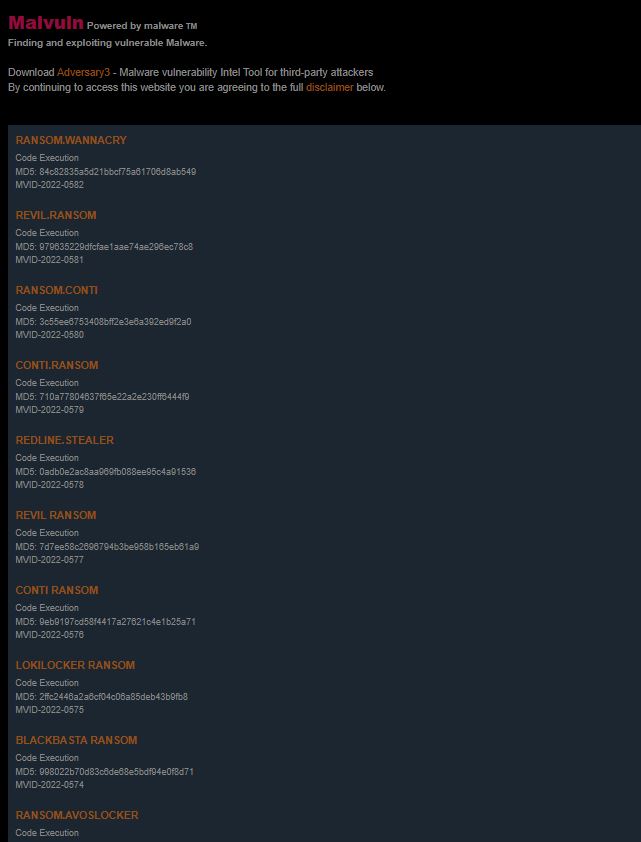
The expert produced a report describing the type of vulnerability found for each affected malware sample, in addition to the sample hash, a proof-of-concept (PoC) exploit, and a demo video. It is worth mentioning that DLL hijacking works only on Windows systems and exploits the way applications search for and load the Dynamic Link Library (DLL) files they require.
A vulnerable program can load a DLL from a path outside its directory, allowing privilege escalation attacks and malicious code execution. According to hyp3rlinx, the exploitation of the flaw in the analyzed ransomware variants allows the execution of code to finish the pre-encryption process.
The researcher mentions that this flaw would allow additional protection against ransomware infections to be applied, placing the DLL in a location of potential interest to threat actors. Once the exploit DLL is loaded, the ransomware process is interrupted, preventing data encryption.
This protection can prove highly effective, as although malware can evade security solutions on the target system, it can’t do anything against DLLs, as they are just files stored on the host’s disk, and remain inert until they are loaded. It is unclear which versions of these ransomware variants are affected by this attack, although it is estimated that this method will only be functional for a short time, as these ransomware operations will surely update their code to address the error.
On previous occasions, hyp3rlinx has filed similar reports about security issues in malware variants. In his latest report, the expert detailed multiple bugs in RedLine, an information stealing malware capable of harvesting web browsers, messaging platforms, FTP clients and cryptocurrency wallets.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











