The Money Message extortion group attacked MSI in March, claiming to have taken 1.5TB of data. Firmware, source code, and databases were all included in this material. When the $4 million ransom demand was not met, the ransomware organization began distributing the stolen material on their data leak website. The source code for the firmware used in MSI’s motherboards was included in the stolen information from the corporation. Additionally, the compromised source code included the Intel Boot Guard private keys for 116 MSI devices as well as the image signing private keys for 57 MSI products. Modern Intel hardware must include Intel Boot Guard, a crucial security feature intended to stop malicious code known as UEFI rootkits from loading. It is essential for ensuring that Windows UEFI Secure Boot criteria are met. Malicious firmware may remain long after an operating system is restored, disguise its operations from the kernel and security applications, and help spread malware on infected devices.
A firmware image’s validity is confirmed by Intel Boot Guard by determining if it was signed with a legitimate private signing key and an embedded public key in the Intel hardware. The firmware may only be loaded into the device once it has been confirmed. In such case, the firmware is disabled. The recent disclosure of private keys related to the Intel Boot Guard security feature is being aggressively investigated by Intel. The public keys required to validate software signed with the disclosed keys are thought to be integrated into Intel hardware, which makes the released keys a serious issue. On devices employing the disclosed keys, the security feature’s dependability is at risk unless these keys cannot be changed.
On Twitter, Binary posted a warning about the possible effects of the stolen keys on the Intel Boot Guard system. According to the alert, an attacker may be able to sign modified firmware for the impacted devices using the disclosed private keys, circumventing Intel Boot Guard’s verification and making the technology useless.
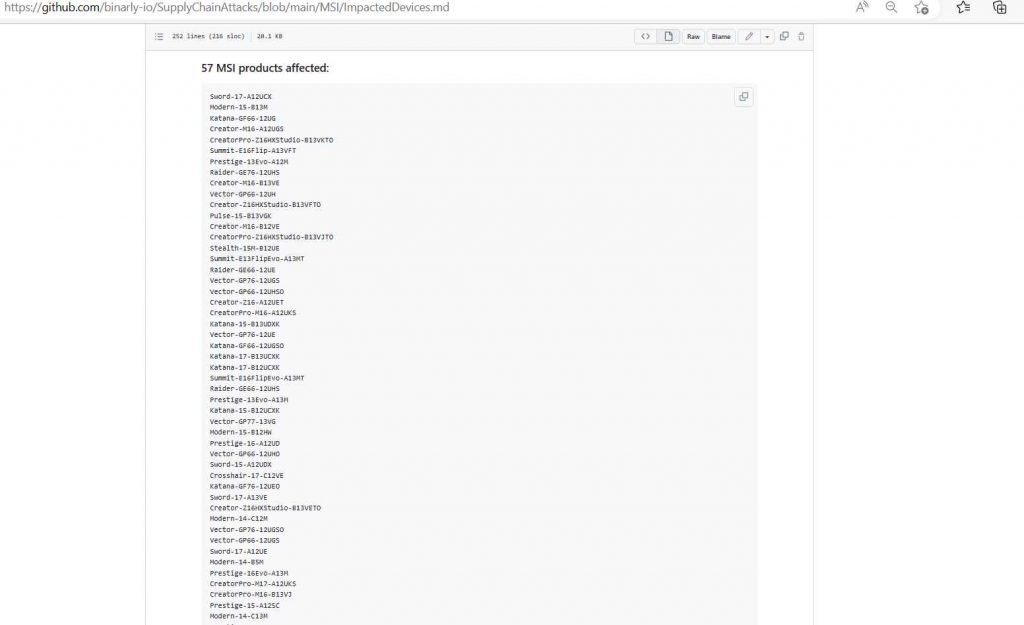
The majority of threat actors may not find use for the exposed keys, but knowledgeable attackers have employed malicious firmware in the past, including the authors of the CosmicStrand and BlackLotus UEFI malware. A list of the 116 MSI products that are supposedly impacted by the stolen Intel Boot Guard keys has been made public by Binary. Given that attackers may now be able to create malicious firmware upgrades on vulnerable devices without worrying about being discovered by the security feature, the leak emphasizes the urgent need for Intel and MSI to solve the possible hole in Intel Boot Guard protection. The breach may have left MSI devices with 11th Tiger Lake, 12th Adler Lake, and 13th Raptor Lake CPUs unable of utilizing Intel Boot Guard.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











