Today many schools, colleges, police departments and even normal people are getting fake calls. Numbers look real sometimes local, sometimes from other states or countries. But in reality, the caller is a scammer or bad guy with not good motive.

Let’s understand how this actually works step by step, and more importantly why each step is needed.
Step 1: They use a calling app (not normal phone)
Scammer starts by opening a calling app on laptop or mobile. This app looks like a normal phone dial pad where they enter the victim’s number. But this app alone cannot make the call it only gives them dialer. Think of it like dialing a number without having network connection yet. Without this, they have no way to dial numbers. If they are using mobile, they don’t want to use mobile phone dialer as that will make call using their own SIM and telecom operator.
Tools used:
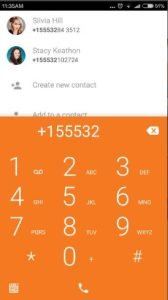
1. Zoiper
Zoiper, the free softphone to make VoIP calls through your PBX or favorite SIP provider. Available for iPhone, Android, Windows Phone 8, Windows, Mac and Linux.
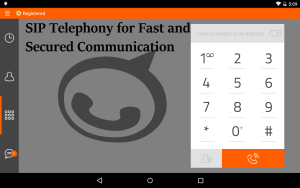
2. Linphone
The Linphone Softphone. For desktop computers, smartphones, and soon in a web version! A fully-featured softphone compatible with third-party VoIP platforms
Important:
This step alone is useless.
👉 App cannot connect calls by itself.
Step 2: They connect to a VoIP system (this is the real engine)
Next, the app connects to a VoIP system, which works like a telephone company on the internet. This system actually sends the call to the real phone network so it can reach the victim. Without this step, the call would never go through. This is the core engine that makes the scam call possible. This is like a telephone company on the internet. It actually connects the call to your phone network. Because Step 1 is only a dial pad.
Tools:
1. Asterisk
Asterisk is a software that turns a computer into a small phone system, like a mini telecom exchange. It helps make and route calls from one person to another. It connects to telecom companies through the internet, and those companies then deliver the call to real mobile numbers like Airtel or Jio.
It connects to telecom providers using internet-based calling (SIP), where you add a provider account (called a SIP trunk), and Asterisk sends calls through that provider, which then connects them to real mobile networks like AT&T, Verizon, Airtel or Jio.
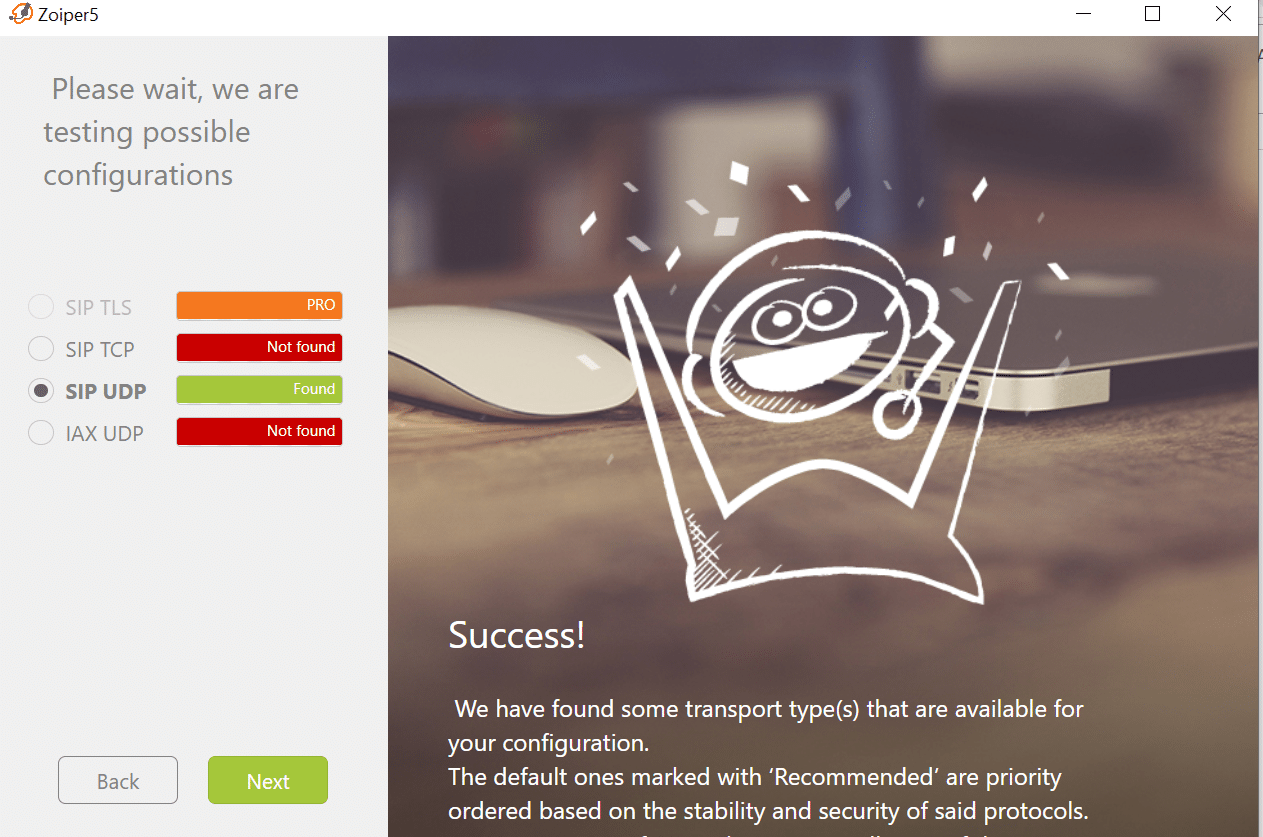
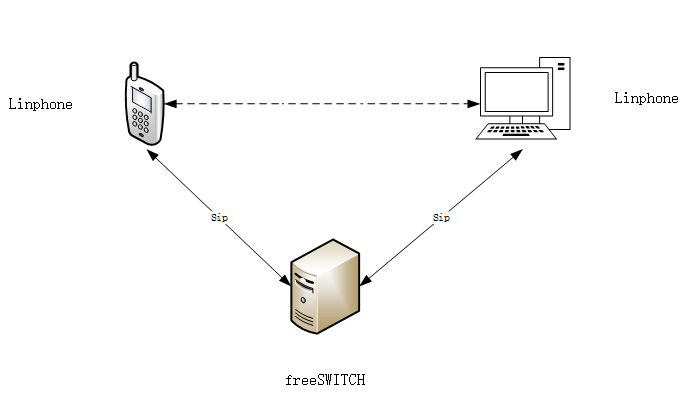
2. FreeSWITCH
FreeSWITCH is a program that lets a computer act like a phone system. It manages calls and sends them to the right place. It connects through internet-based providers, which then deliver the call to normal mobile networks like AT&T, Verizon, Airtel or Jio.
Important:
- Call will never reach victim
- No connection happens
This is the most important step.
Step 3: They change the caller ID (main scam trick)
Before placing the call, the scammer sets a fake number that will appear on the victim’s phone. This could look like a local number, police number, or bank number. This step is very important because it builds trust. The victim sees a familiar number and is more likely to answer.
Tools / platforms:
1. Twilio
Twilio is a cloud-based customer engagement platform that provides APIs (Application Programming Interfaces) allowing developers to integrate voice, messaging (SMS, WhatsApp), video, and email capabilities directly into applications
2. TextNow
TextNow is the only free phone service provider with unlimited talk & text, free data for select apps, and nationwide 5G coverage all in one convenient app.
They can show:
- Indian number
- Police number
- Bank number
- This step = fake identity
Step 4: Landing call to Telecom provider
This step will land call to the victim phone or mobile. Fake number that will appear on the victim’s phone. This could look like a local number, police number, or bank number. So the whole process in which scammers make call is as below:

in Step 1, Scammers use a dialer app to enter numbers and avoid the normal mobile dialer because it uses a SIM and exposes their real number. Scammers use mobile apps, but those apps must be VoIP-based, not the regular SIM dialer.
In Step 2, the dialer app must connect to a VoIP server like Asterisk or FreeSWITCH, which actually makes the internet call possible and acts as the engine of the entire process.
In Step 3, It is not a separate software that converts VoIP to the telecom network; instead, this role is handled by a VoIP provider such as Twilio. This provider acts as a bridge between internet calls (VoIP) and the traditional telecom network (PSTN). This is also the point where the caller ID can be controlled or spoofed.
In Step 4, Scammers do not directly use telecom providers like a SIM. Instead, the VoIP provider sends the call to telecom networks such as AT&T, Airtel or Jio, which then deliver the call to the victim.
The scammer uses a VoIP app to dial the number, the app connects to a VoIP server to create the call, the VoIP provider converts and routes the call to the telecom network while allowing caller ID manipulation, and finally the telecom network delivers the call to the victim.
In simple terms, the full chain is: Dialer → VoIP server → VoIP provider → Telecom → Victim
Now below steps are optional and are used to hide scammer identity from Law Enforcement agencies
Step 5 (Optional): Call is routed through multiple systems
The call is not sent directly to the victim. Instead, it passes through multiple servers or networks before reaching the phone. Each step adds distance between the scammer and the victim. This makes it difficult to trace where the call originally came from.
Tools:
It goes like this:
Attacker → Server 1 → Server 2 → Telecom → You
Why this step is needed:
- Hides the real source
- Makes tracing harder
- Like passing through many cities before reaching you
Step 6 (Optional): They hide their location
Scammer hides their real location using tools like VPN or other privacy networks. So even if someone checks the system logs, they will only see a different location, not the real one. This adds another layer of protection and makes investigation harder.
Tools:
This step = extra safety for attacker
Step 7 (Optional): They find or use weak systems
Sometimes scammers don’t use their own system at all. They find weak or poorly secured VoIP systems and use them to make calls. This way, even if the call is traced, it leads to an innocent system owner, not the real attacker. This makes tracking the real person much more difficult.
Tool:
What this step does:
- Finds poorly secured VoIP systems on internet.
- Instead of using their own system:
Think like this:
Step 1 → You pick up phone
Step 2 → Network connects call
Step 3 → You wear fake identity
Step 4 → You travel through many routes
Step 5 → You hide your home address
Step 6 → You use someone else’s phone
Final result:
- Victim sees a fake number
- Police sees multiple layers
- Real person is hidden behind all this

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.