Worldwide universities attacked by North Korean hackers
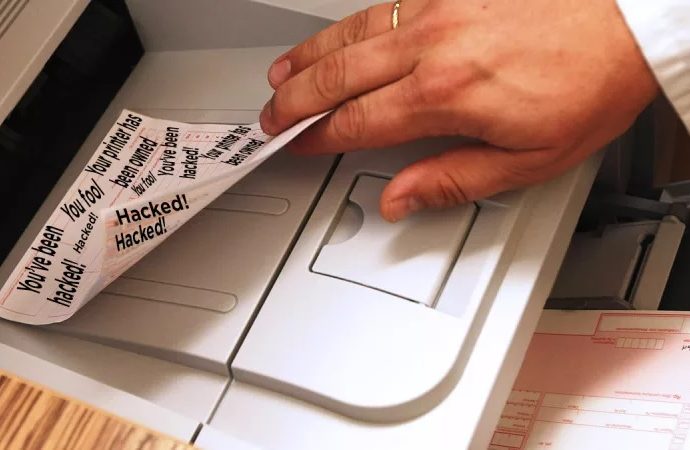
Academic organizations around the world have been attacked since last May Digital forensics specialists from the International Institute of Cyber Security report that hacker groups linked to North Korea haveRead More →