Iranian hackers shut down 28 Israeli railway stations; they had plans to collide trains
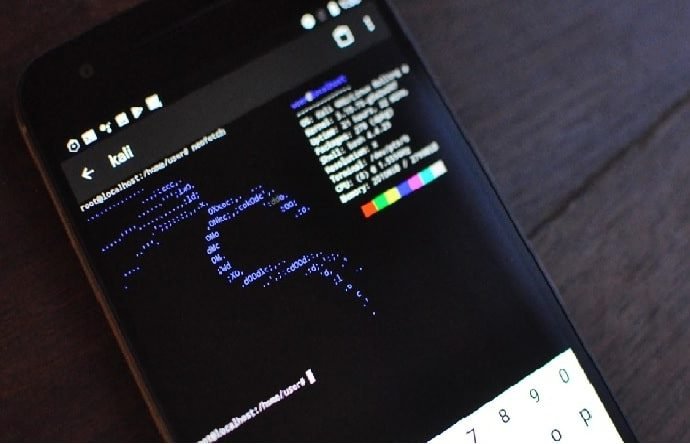
Hacking campaigns between the governments of Israel and Iran continue to increase, as mentioned by information security awareness specialists. According to recent reports, a group of Iranian hackers would haveRead More →