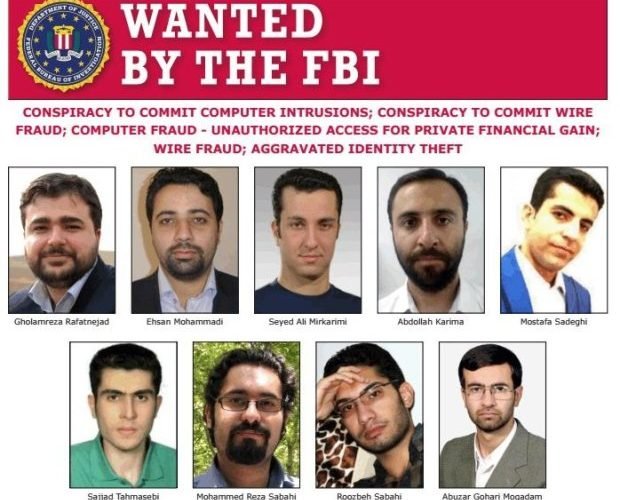
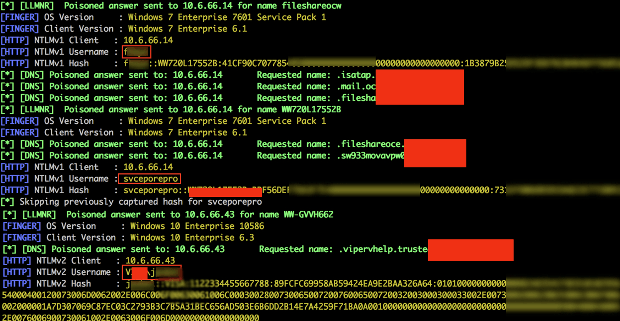
Nine Iranians indicted by US for hacking to steal research data
“Password spraying” attack gave Mabna group access to 32TB of diverse research data. Today, the Department of Justice announced charges against nine Iranian nationals connected to the Mabna Institute, a company an FBIRead More →