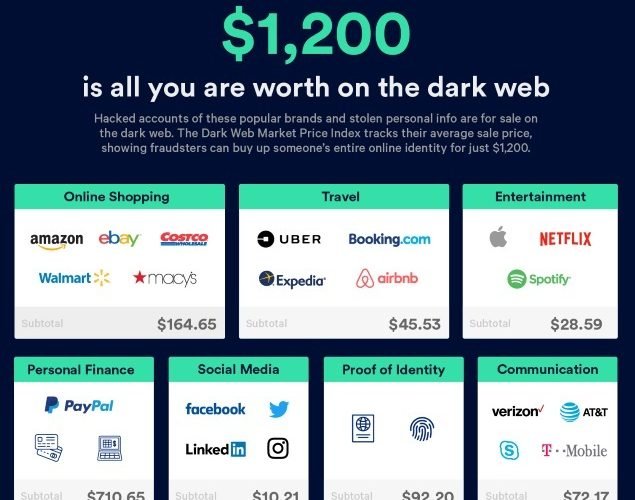
VPN HotSpot Shield, PureVPN and ZenMate are revealing real IP addresses
According to VPN Mentor, a private firm which reviews virtual private networks (VPN), after research, it has been discovered that three VPN service providers with millions of customers worldwide areRead More →