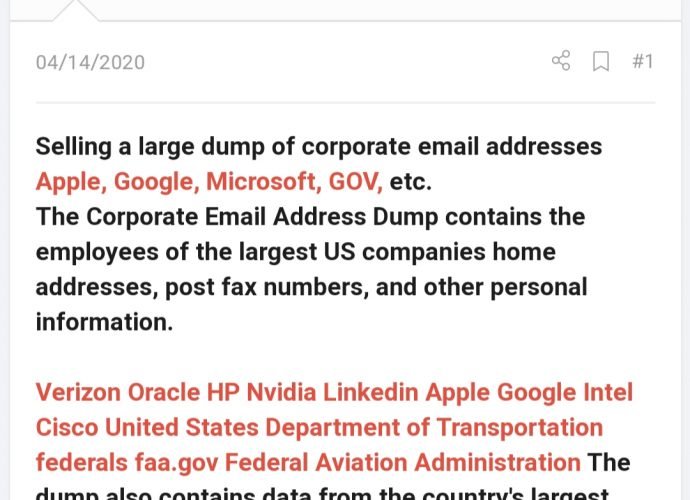
Employee data leaked: Apple, Google, Microsoft,LinkedIn, Intel Cisco, Verizon, Oracle, HP, Nvidia affected
Cyber forensics research team has found a sale of database containing 2GB of records detailing information on employees of big corporate companies like Apple, Google, Microsoft, LinkedIn, Intel Cisco, Verizon,Read More →