SIEMENS PATCHES CRITICAL INTEL AMT FLAW IN INDUSTRIAL PRODUCTS
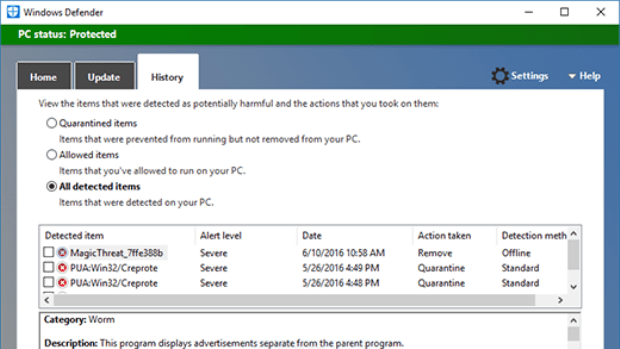
Siemens patched two critical vulnerabilities that affected its industrial products this week. One, tied to a recently disclosed flaw in Active Management Technology – a function of certain Intel processorsRead More →