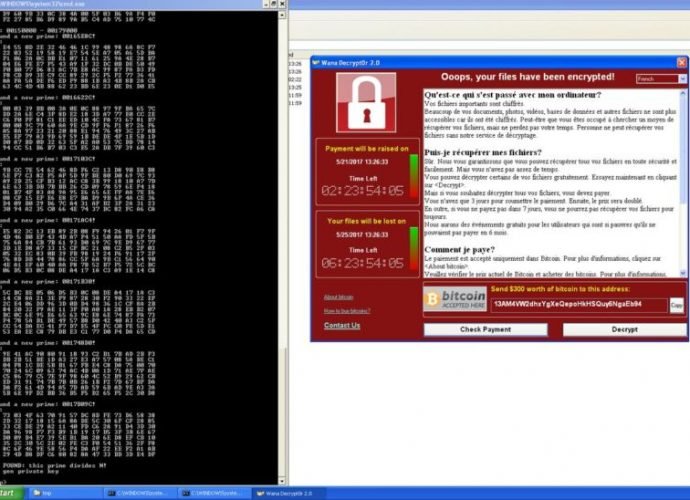
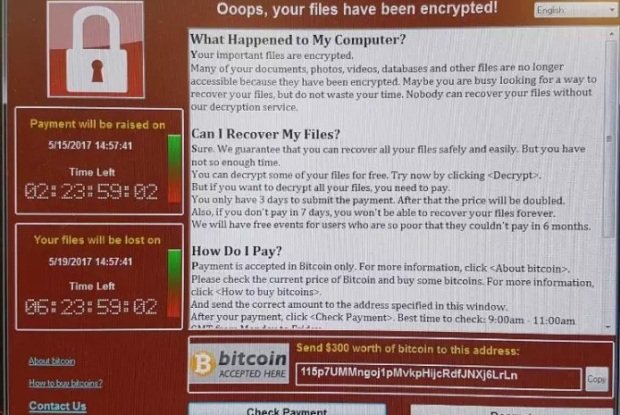
Windows XP PCs infected by WCry can be decrypted without paying ransom
Decryption tool is of limited value, because XP was unaffected by last week’s worm. Owners of some Windows XP computers infected by the WCry ransomware may be able to decryptRead More →