Researchers expose Mirai vuln that could be used to hack back against botnet
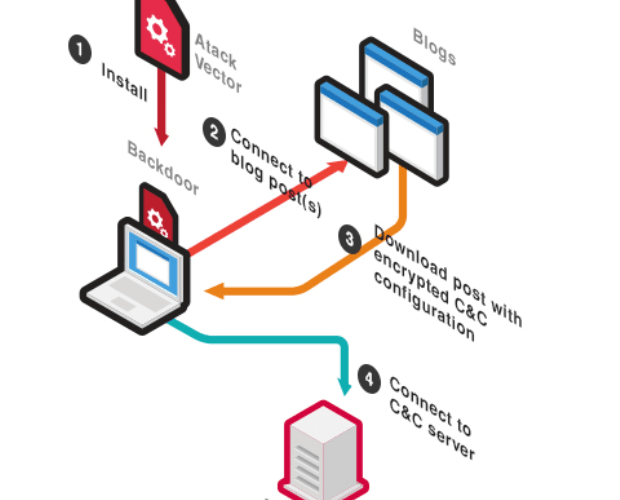
Security researchers have discovered flaws in the Mirai botnet that might be used to mitigate against future attacks from the zombie network. Scott Tenaglia, a researcher at endpoint security firmRead More →