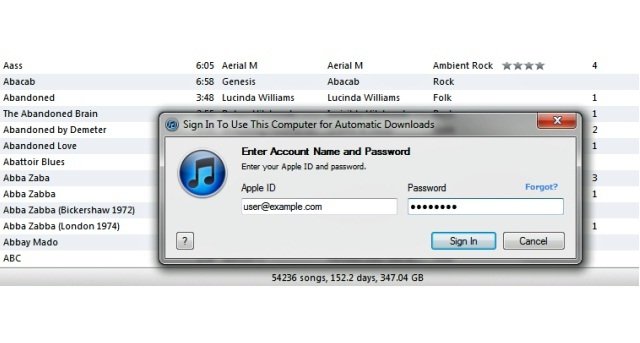
Malware infecting jailbroken iPhones stole 225,000 Apple account logins
A newly discovered malware family that preys on jailbroken iPhones has collected login credentials for more than 225,000 Apple accounts, making it one of the largest Apple account compromises toRead More →