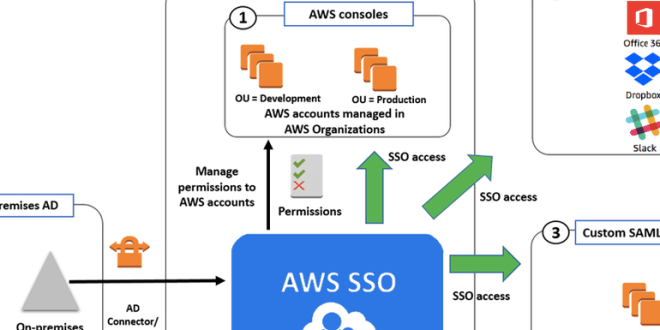
Amazon launches single sign-on service for AWS cloud
AWS SSO will let users manage access to multiple AWS accounts and applications using their existing corporate credentials. Amazon Web Services’ re:Invent conference is wrapped up and in the bag,Read More →