4G/5G Wireless Networks as Vulnerable as WiFi and putting SmartCities at Risk
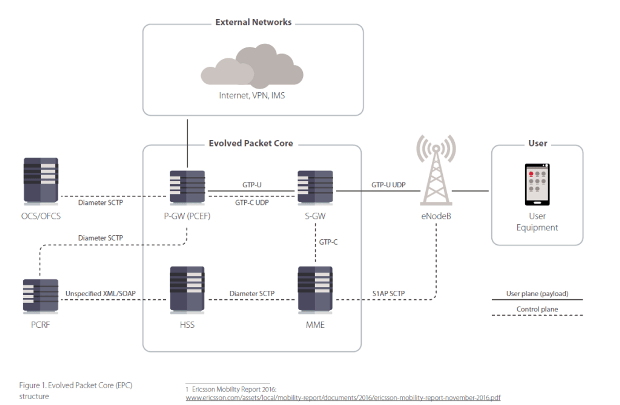
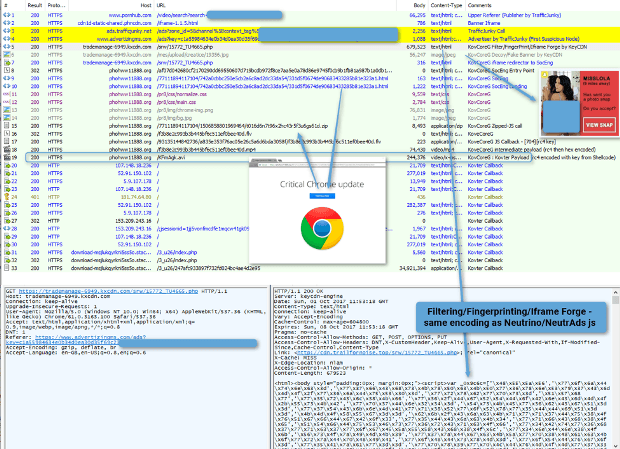
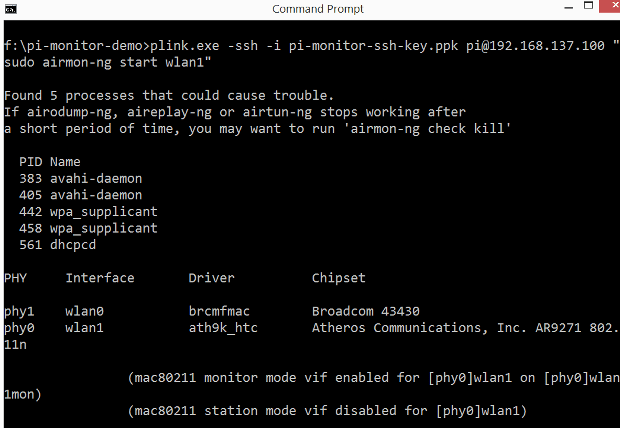
Researchers from security firm Positive Technologies warns of 4G/5G Wireless Networks as vulnerable as WiFi and putting smart-cities at risk The Internet of Things (IoT) presents many new opportunities and some differentRead More →