2016’s Most Popular Exploit Was the Vulnerability Used for the Stuxnet Attacks
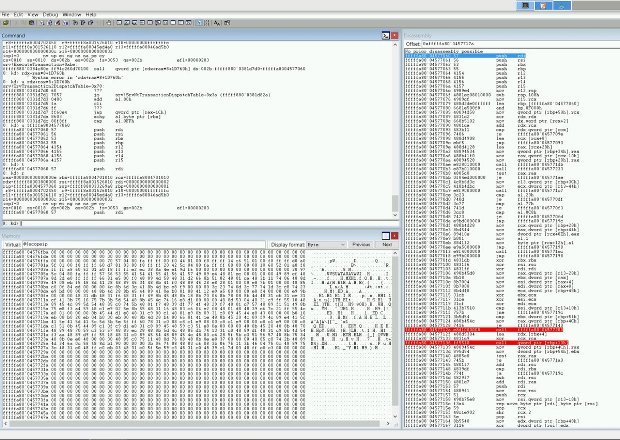
One of the vulnerabilities used to spread the Stuxnet virus was 2016’s most popular exploit, according to telemetry data gathered by Russia cyber-security firm Kaspersky Labs. Identified as CVE-2010-2568, thisRead More →