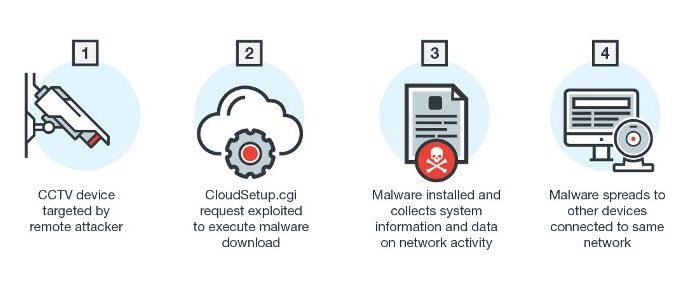
New Linux Malware Exploits CGI Vulnerability
Linux has long been the preferred operating system for enterprise platforms and Internet of Things (IoT) manufacturers. Linux-based devices are continually being deployed in smart systems across many different industries,Read More →