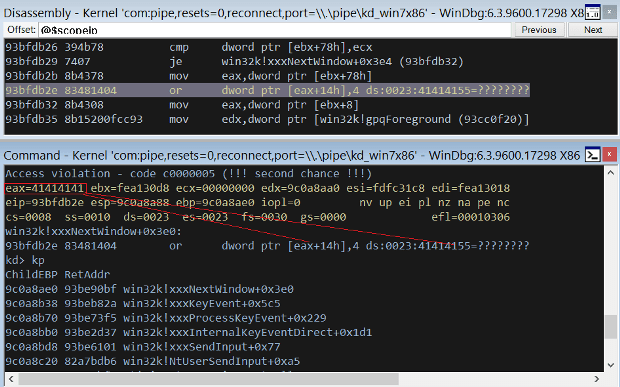
Digging Into a Windows Kernel Privilege Escalation Vulnerability: CVE-2016-7255
The Windows kernel privilege escalation vulnerability CVE-2016-7255 has received a lot of media attention. On November’s Patch Tuesday, Microsoft released a fix for this vulnerability as part of bulletin MS16-135.Read More →