The DNC keeps the Watergate file cabinet next to server hacked by Russia
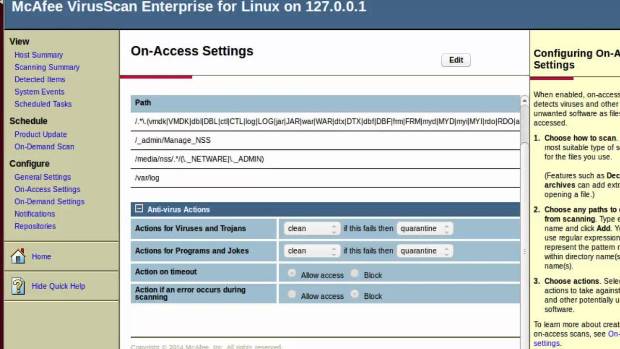
The basement of the Democratic National Committee’s Washington, DC, headquarters holds one of the most fitting images to come out of the hacks that dogged Democrats in the 2016 presidentialRead More →