Reversing and Exploiting Embedded Devices (Walking the software and hardware stack)
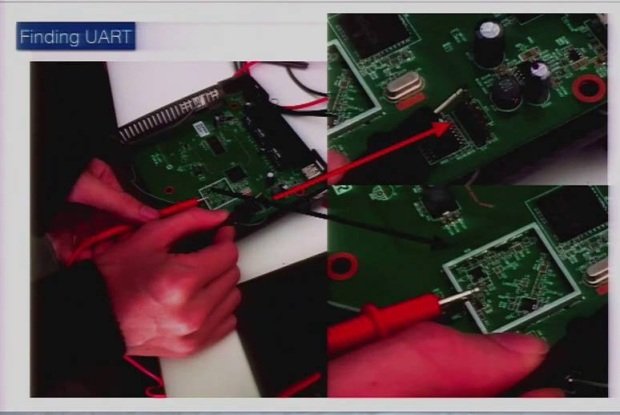
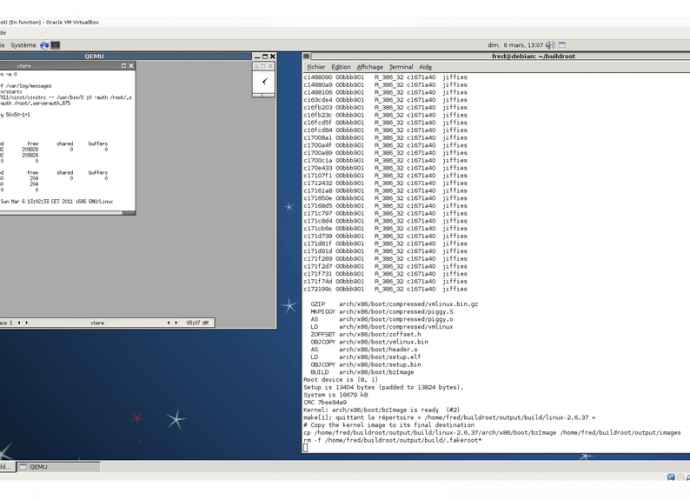
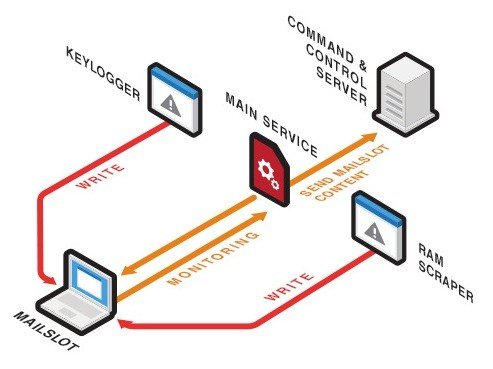
As technology matures and microprocessors are becoming cheap we are starting to see a trend of products that are now ?smart.? The problem is that once we discover how theseRead More →